Setting up your identity provider
After signing in for the first time with your EDB account, you can either use the BigAnimal portal as your identity provider or set up your own.
Note
If you purchased through Azure Marketplace, BigAnimal authenticates users using Azure Active Directory (AD) and you don't have to complete these steps. Azure AD is linked during subscription. Also, you can still invite users that have an EDB account through the BigAnimal portal.
When using your own identity provider, you add users to BigAnimal by adding them to the designated group in your identity provider. Once you've logged into BigAnimal using your own identity provider, you can set up your cloud service provider in the BigAnimal portal to complete onboarding.
If you're using the BigAnimal portal as your identity provider, you can also invite users that have an EDB account by selecting Invite New User on the Users page. After providing their EDB account email and their role, you can send them an invitation link. Ensure the user accepts the invitation within 48 hours, or you'll have to send a new invitation.
For more information on roles, see Managing portal access.
Setting up your own identity provider
BigAnimal supports single sign-on through SAML identity providers. The SAML application enables access to BigAnimal for groups selected in your identity provider. You configure your SAML application to send a SAML assertion response to BigAnimal for each user.
The identity provider application provides:
- Signature certificate
- Single sign-on URL (Sign In Endpoint)
The BigAnimal service provider provides:
- ACS URL (Assertion Consumer Service)
- SP Entity ID (Audience URI)
The Set Up Identity Provider page in BigAnimal provides the ACS URL and Audience URI, which you can copy to use when configuring your SAML application. The page also includes information about mandatory attributes for the configuration.
You need the following SAML assertions to map the user information in your identity provider application to BigAnimal:
http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier http://schemas.xmlsoap.org/ws/2005/05/identity/claims/name http://schemas.xmlsoap.org/ws/2005/05/identity/claims/givenname http://schemas.xmlsoap.org/ws/2005/05/identity/claims/surname http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress
Configure SAML
On the Set Up Identity Provider page:
In the Connection Info section, copy the following URLs to use in your identity provider configuration:
URL Description Assertion Consumer Service URL BigAnimal-specific URL to which SAML assertions from your identity provider are sent Audience URI The entity or audience for which the SAML assertion is intended In the Configure SAML response section, configure your identity provider to send the SAML response. The SAML response must include the following attributes:
givenname— BigAnimal uses the value as the given name in the profile of the authenticated user.surname— BigAnimal uses the value as the surname in the profile of the authenticated user.name— BigAnimal uses the value as the full name (givennamejoined withsurname) in the profile of the authenticated user.emailaddress— BigAnimal uses the value for the email address in the profile of the authenticated user.
Provide a
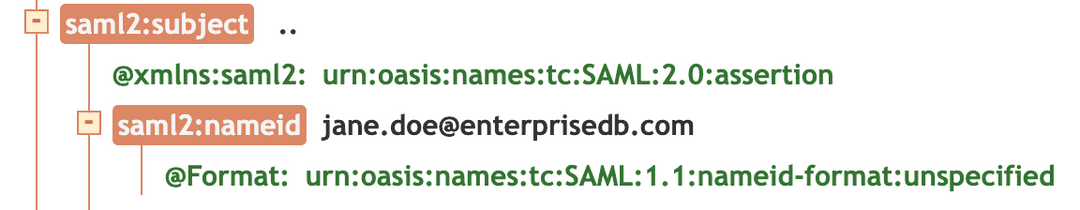
NameIDelement in theSubjectelement. Provide your email ID as the value toNameID. BigAnimal uses the email ID you provide as your username and primary email, so formatNameIDlike an email address.For example:
In the SAML settings section, enter the configuration information for your preferred SAML identity provider:
Field Description Single Sign-On URL The identity provider's sign-on URL. Identity Provider Signature Certificate Identity provider's assertion signing certificate ( .ceror.cert). Coordinate with your identity provider partner to obtain this certificate securely.Request Binding SAML Authentication Request Protocol binding used to send the authentication request: HTTP-Redirect, HTTP-Post, or Hybrid (SAML request is REDIRECT and response is POST). Response Signature Algorithm (RSA) Algorithm The signature algorithm used to sign the SAML AuthNRequest (RSA SHA-1 or RSA SHA-256). Select Test Connection. If you connect to your identity provider successfully, your identity provider's login screen appears. If an error message appears, contact Support.
Once your identity provider is set up, you can view your connection status, ID, login URL, audience URI, and assertion consumer service URL from the BigAnimal portal on the Identity Provider page. Select Admin > Identity Provider to access it.
Further reading
Add a domain
You need a verified domain so your users can have a streamlined login experience with their email address.
On the Domains tab, enter the domain name and select Next: Verify Domain.
To add it as a TXT record on that domain in your DNS provider's management console, copy the TXT record and follow the instructions in the on-screen verify box:
- Log in to your domain registrar or web host account.
- Navigate to the DNS settings for the domain you want to verify.
- Add a TXT record.
- In the Name field, enter
@. - In the Value field, enter the verification string provided, for example,
edb-biganimal-verification=VjpcxtIC57DujkKMtECSwo67FyfCExku. - Save your changes and wait for the DNS propagation period to complete. This can take up to 48 hours.
Select Done.
Your domain and its status appear on the Domains tab, where you can delete or verify it. Domains can take up to 48 hours for the change of the domain record by the DNS provider to propagate before you can verify it.
If your domain hasn't verified after a day, you can debug whether your domain has the matching verification text field. o check the exact value of the required TXT field, select Verify next to the domain at
/settings/domains. Query your domain directly with DNS tools, such as nslookup, to check if you have an exact match for a text = "verification" field. Domains can have many TXT fields. As long as one matches, it should verify.
> nslookup -type=TXT mydomain.com ;; Truncated, retrying in TCP mode. Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: ... mydomain.com text = “edb-biganimal-verification=VjpcxtIC57DujkKMtECSwo67FyfCExku”
To add another domain, select Add Domain.
When you have at least one verified domain (with Status = Verified, in green), the identity provider status becomes Active on the Identity Providers tab. When the domain is no longer verified, the status becomes Inactive.
Note
Your DNS provider can take up to 48 hours to update. Once the domain is verified, the identity provider status can take up to three minutes to update.
Domain expiry
The EDB system has a 10-day expiry set for checking whether domains are verified.
You buy domains from DNS providers by way of a leasing system. If the lease expires, you no longer own the domain, and it disappears from the Internet. If this happens, you need to renew your domain with your DNS provider.
Whether the domain failed to verify within the 10 days or it expired months later, it appears as Status = Expired (in red). You can't reinstate an expired domain because expiry means you might no longer own the domain. You need to verify it again.
- To delete the domain, select the bin icon.
- To re-create the domain, select Add Domain. Set a new verification key for the domain and update the TXT record for it in your DNS provider's management console, as described in Add a doman.
Manage roles for added users
You add users through your identity provider. A user who you add in the identity provider is automatically added to BigAnimal. BigAnimal assigns them with the default role of organization member. You manage roles and permissions from BigAnimal. See Managing portal access.
Note
A user is created in BigAnimal only after they log in. After they log in, you can change their BigAnimal role.
Add a tile
Once you establish the identity provider, you can create a BigAnimal tile for users to access the organization's BigAnimal application. To do so, copy the quick sign-in URL from the Settings > Identity Provider page of the BigAnimal portal. For details on how to add a tile, refer to your identify provider documentation for instructions on setting up SSO access to your application.
Next steps
You and other users can log in to BigAnimal using your identity provider credentials.
You can rename the default project BigAnimal creates for you. See Editing a project.
You can set up your cloud service provider so that you or other users with the correct permissions can create clusters.
You can assign roles to your default project. See Managing portal access.
- On this page
- Setting up your own identity provider
- Next steps