The End of the Monolithic Image: Dynamic Extensions in Kubernetes with PostgreSQL 18
At EDB, we are constantly pushing the boundaries of what is possible with your database server, especially in the AI space. As organizations scale, they require systems that not only handle immense workloads but also embrace the core principles of the cloud: immutability, declarative management, and decoupled architecture.
However, for years, one persistent operational hurdle has slowed the adoption of complex, modern workloads like AI/Vector services in Kubernetes: the tension between powerful extensibility and strict immutability.
In this post, I want to explore a foundational breakthrough in the upcoming PostgreSQL 18 and EDB Postgres® AI (EDB PG AI) releases that resolves this tension. By leveraging a dual-layer innovation—spanning both the database core and the Kubernetes orchestration layer—we are ushering in a new era where extensions are dynamic, secure, and truly cloud-native.
For the enterprise, this translates directly to agility: instead of delaying a critical AI launch by weeks to rebuild monolithic database images, teams can now deploy high-value capabilities like pgvector in minutes, accelerating time-to-market while maintaining a rock-solid security posture.
The Operational Barrier: When Extensibility Meets Immutability
PostgreSQL's extensibility is one of its greatest strengths, allowing for the integration of powerful tools such as PostGIS, TimescaleDB, and pgvector. However, the operational complexity of managing these extensions within cloud-native environments like Kubernetes has historically been a source of friction.
Our core strategy at EDB is built on non-negotiable best practices: specifically, immutable infrastructure. This fundamental Kubernetes principle demands that container images remain strictly read-only after deployment.
The traditional path to extension management created significant operational drag:
- Monolithic Images: The only way to run third-party extensions was to embed them directly into the PostgreSQL operand image.
- High Overhead: This resulted in bloated image sizes and rigid extension selection.
- Security Debt: Users were forced to maintain custom images, embedding unnecessary libraries that inflated the security surface and complicated the tracking of CVEs.
We needed a way to achieve dynamic extension loading while strictly adhering to our immutability principle. The monolithic alternative was unsustainable, turning every feature request into a risky, sluggish full-stack rebuild.
The Breakthrough: Dual Innovation in PostgreSQL 18 and Kubernetes 1.33
We are thrilled that these key improvements are now emerging, paving the way for the entire cloud-native stack.
1. Decoupling Extensions in PostgreSQL Core: extension_control_path
The extension control path is the directory and mechanism by which PostgreSQL and EDB PG AI Database locate control files for extensions. These files are essential metadata that define how an extension is installed, its version, and its dependencies.
Default control files must be placed in the installation’s SHAREDIR/extension directory. In an immutable environment like CloudNativePG, this standard directory is read-only, preventing runtime installation.
Our elite experts at EDB successfully developed and proposed a crucial patch for PostgreSQL 18 that addresses this. This patch introduces the new configuration option (GUC), extension_control_path. This option allows users to specify multiple, additional directories for extension control files.
This seemingly simple change is transformative. It allows PostgreSQL to locate extension control files and shared libraries from multiple, non-system-wide directories, effectively decoupling the extension from the core server image. This results in drastic operational simplicity thereby reducing complexity and operational costs.
2. Immutable Mounting with Kubernetes ImageVolume
While the database can now look in new places, we needed a way to dynamically introduce the extension files without modifying the primary container image.
Kubernetes innovation delivers this with the ImageVolume feature, expected to reach beta in Kubernetes 1.33. ImageVolume allows us to mount a container image as a read-only and immutable volume inside a running pod.
This allows us to package PostgreSQL extensions as independent, Open Container Initiative (OCI)-compliant container images and mount them into CloudNativePG clusters at known directories.
3. Deep Dive: The Anatomy of a Dynamic Extension
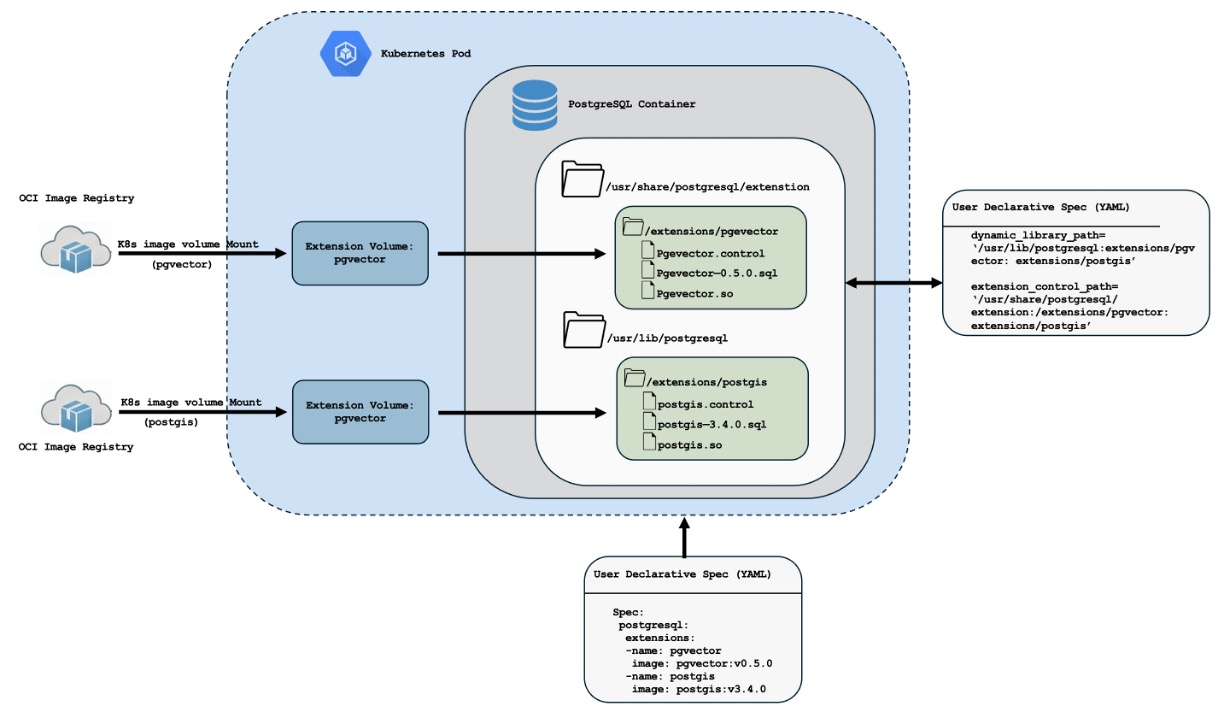
To understand how we maintain strict immutability while allowing runtime flexibility, let’s trace the flow of data illustrated in the architecture diagram below.
3.1 The Trigger: Everything begins with the user's intent. Instead of writing complex scripts, you simply define the needed extensions in .spec.postgresql.extensions section of your Cluster manifest. This declarative approach ensures that your requirements are versioned and reproducible.
3.2 The Source: OCI-Based Decoupling Extensions are no longer buried inside the monolithic database image. Instead, they are packaged as independent, minimal OCI-compliant images (e.g., a lightweight pgvector container) stored in your registry. This effectively decouples the extension lifecycle from the core database lifecycle.
3.3 The Mechanism: The CloudNativePG operator leverages the Kubernetes ImageVolume feature to pull these artifacts. Crucially, it does not "install" them in the traditional sense; it mounts the extension image as a read-only volume directly into the Pod. This ensures the core PostgreSQL container remains untouched and immutable.
3.4 Secure Isolation: Inside the container, the extension files land in specific, isolated directories rather than the system-wide path. This keeps the system path clean and ensures that different extensions do not conflict with the core server files.
3.5 Dynamic Configuration: Finally, the operator bridges the gap between the filesystem and the database. It dynamically updates the new PostgreSQL 18 extension_control_path and the existing dynamic_library_path GUCs. This configuration allows PostgreSQL to "see" and load control files from these new, mounted locations as if they were native to the system.
4. CloudNativePG: Enabling Declarative, Dynamic Management
The CloudNativePG Operator automates seamless integration, turning manual operations into declarative code:
- OCI Artifacts: Extensions are packaged as minimal OCI images (e.g., a lightweight pgvector image of only 1.6MB).
- Declarative Deployment: Users simply define required extensions in the spec.postgresql.extensions section of the Cluster manifest.
- Automated Configuration: The operator mounts the image as a read-only volume and updates the PostgreSQL GUCs (dynamic_library_path and extension_control_path) to include the mounted paths.
5. Strategic Impact: Your ROI
This technical decoupling is not just an operational fix. It delivers significant, measurable business value by accelerating time to market and reducing complexity:
- Accelerating Time-to-Market (Agility): Dynamic installation of extensions drops deployment time from weeks to minutes, accelerating the launch of new, high-value features (e.g., AI/Vector search).
- Promoting Security & Compliance Resilience: Core database images remain minimal and stable when extension patches are applied independently they reduce the attack surface and minimize the duration of maintenance windows.
- Driving Operational Efficiency: By eliminating the need for maintaining a proliferation of custom, monolithic PostgreSQL images this frees up expensive Platform Engineer hours that can now focus on strategic architecture initiatives rather than low-value maintenance tasks.
Best Practices for the New Era
As we move toward this decoupled future, adherence to core extension management, these best practices remains vital:
- Security First: Avoid marking extensions as trusted unless absolutely necessary, and rigorously secure installation scripts to prevent privilege escalation.
- Schema Flexibility: For relocatable extensions, avoid hard-coded schema references and use @extschema@substitution in scripts.
- OCI Compliance: For Kubernetes environments, EDB recommends publishing OCI-compliant extension images with a standard layout (share and lib directories) for compatibility.
Conclusion
The alignment of PostgreSQL 18's configurable extension paths and Kubernetes 1.33's ImageVolume is a landmark moment. This breakthrough ensures that EDB PG AI deployments remain the industry standard for enterprise-grade, cloud-native database management.
By embracing OCI images as first-class artifacts for extensions, we are delivering an EDB Postgres experience in Kubernetes that is both immutable and flexible, just as it should be. Contact us if you have more questions about optimizing your Postgres on Kubernetes strategy.
References
To learn more more about this exciting new capability for Kubernetes, read this article by Gabriele Bartolini.